What Is Multi-Tenant Architecture A Guide to SaaS Scalability
Discover what is multi-tenant architecture and how it drives modern SaaS. Learn about tenancy models, benefits, and security for building scalable applications.
published
Outrank AI
multi-tenant architecture, saas architecture, cloud tenancy, data isolation, saas scalability
5f9384dd-4dc2-4c52-beb4-274ab35d9d78
At its heart, multi-tenant architecture is a software design where one application serves many customers—or tenants, as they're called. Think of it as the backbone of nearly every modern Software-as-a-Service (SaaS) platform you use, from Salesforce to Slack.
Even though everyone shares the same software and infrastructure, each tenant's data is kept completely separate and secure. It's a simple concept with a powerful impact.
The Apartment Building Analogy for Multi-Tenancy
To really get a feel for multi-tenancy, let's ditch the technical jargon for a minute and think about real estate.
Imagine you're building a new software application. One way to go is to build a separate, single-family house for every customer. We call this single-tenancy. Each customer gets their own plot of land, their own foundation, and their own utilities. This gives them total privacy and control, but it's wildly expensive and a nightmare to maintain. Need to fix a leaky pipe? You have to drive out to every single house to do it.
Now, let’s flip the script and think like a multi-tenant developer. Instead of dozens of separate houses, you build one large apartment building. This single structure can house hundreds of different tenants, each living in their own secure, private unit.
Key Takeaway: In this model, all the tenants share the building's core infrastructure—the foundation, the plumbing, the electrical grid, and the security system. Sharing these resources drives down costs for everyone, from the landlord (that's you, the software provider) to the tenants (your customers).
This is exactly how multi-tenant architecture works. You build and maintain one application (the building), and all your customers (the tenants) use it at the same time, with their data safely isolated in their own virtual "apartment."
Core Principles of Multi-Tenant Architecture
This shared approach is so effective because it’s built on a few key ideas. These principles are especially crucial in applications that manage complex data pipelines. If you're just diving into this world, understanding the modern analytics stack can give you great context for where multi-tenancy really shines.
Here’s what makes the model tick:
Shared Resources: One database, one server, and one application instance can support all your customers. This efficiency translates directly into major cost savings.
Data Isolation: Even though resources are shared, strict security ensures one tenant can never peek into another's data. It’s non-negotiable.
Centralized Maintenance: When you need to push an update, fix a bug, or roll out a new feature, you do it just once. The changes are instantly available to every single tenant.
Scalability: Adding a new customer is as easy as renting out another apartment. You can grow your user base without having to provision a whole new set of infrastructure each time.
For a clearer picture, let's put these two models side-by-side using our apartment analogy.
Multi-Tenancy vs Single-Tenancy at a Glance
This table breaks down the core differences in a way that’s easy to digest.
Concept | Multi-Tenant (Apartment Building) | Single-Tenant (Single-Family House) |
|---|---|---|
Infrastructure | One building with shared foundation, plumbing, and electrical systems. | Each house has its own dedicated foundation and utilities. |
Cost | Lower operational costs due to shared resources and maintenance. | Higher costs per customer due to dedicated infrastructure. |
Maintenance | A single update (e.g., upgrading the building's water heater) benefits all tenants. | Maintenance must be performed individually for each house. |
Onboarding | A new tenant can move into an available apartment quickly. | A new house must be built from scratch for each new customer. |
Ultimately, the apartment model just makes more sense for most modern software companies. It’s more efficient, scalable, and cost-effective—benefits that get passed down to both the provider and the customer.
Exploring the Three Core Multi-Tenancy Models
When you're building a multi-tenant application, your first major crossroad is deciding how to handle each customer's data. This isn't just a technical detail; it's a foundational choice that impacts cost, complexity, and security for the life of your product. There's no single "best" way—it's all about trade-offs.
Think of the options as a spectrum, from everyone sharing the same space to everyone getting their own private building. Let's walk through the three main approaches.
This diagram shows the basic idea: one central application, one set of infrastructure, serving multiple customers who are kept logically separate from one another.
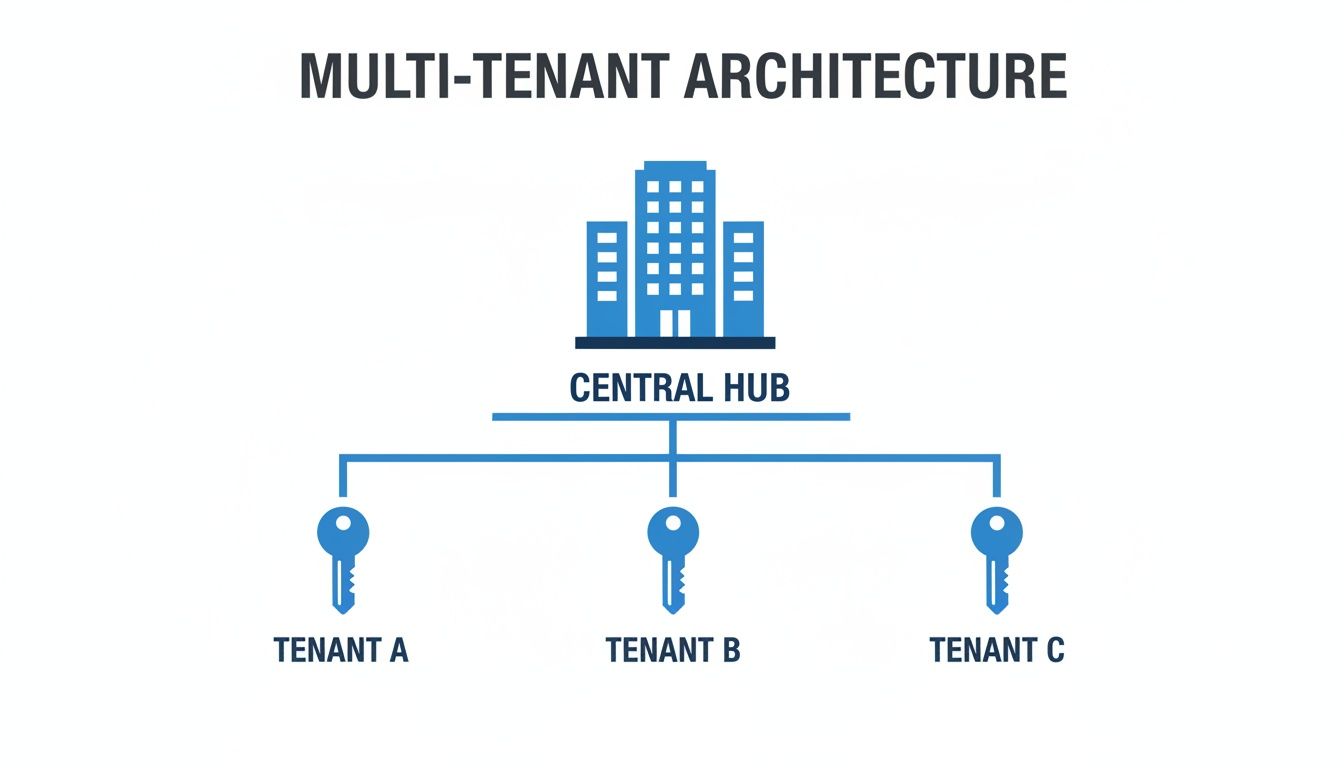
This shared-but-separate concept is the heart of multi-tenant architecture. The real trick is in how you enforce that separation.
The Shared Schema Model
The Shared Schema model is the most popular starting point, especially for SaaS startups. Imagine a giant, open-plan office. Everyone works in the same room (a single database) and uses the same desks and equipment (the database tables).
To keep things organized, every piece of work has a label on it identifying which company it belongs to. In the database world, this means every single row in a table gets a tenant_id column. When a user from "Tenant A" logs in, the application has to be smart enough to add WHERE tenant_id = 'A' to every single database query to pull only their data.
It's incredibly cost-effective because you're maximizing your resource usage. One database serves everyone. The big risk? It puts all the pressure on your code. One tiny mistake in a query—one forgotten WHERE clause—and you could accidentally leak one tenant's data to another.
The Isolated Schema Model
Moving up a step in privacy, we have the Isolated Schema model. Let's go back to our office analogy. This is like giving each company their own private, locked office on the same floor. The building itself and its core services (the database server) are still shared, but the data is neatly partitioned.
Here, every tenant gets their own dedicated set of tables inside a unique "schema" within the same database instance. This gives you a stronger logical wall between tenants. Your application connects to the one database but then switches its focus to the specific schema for that user's session.
This makes development a bit easier, as you no longer need to remember the tenant_id filter everywhere. It also opens the door to customizing the data structure for specific high-value clients. The trade-off is a bit more operational overhead—managing hundreds or thousands of individual schemas requires good automation.
The Isolated Instance Model
At the far end of the spectrum is the Isolated Instance model, which offers maximum separation. This is the equivalent of giving each tenant their own private floor, or even their own building. Each customer gets a completely separate database running on its own dedicated server or container.
This approach provides the ultimate security and isolation. With no shared database resources, the risk of data leakage between tenants is virtually zero. It also solves the "noisy neighbor" problem, where a power user from one company could slow down the application for everyone else. This is why you often see this model used for enterprise-grade customers or in heavily regulated industries like finance and healthcare.
Market data reflects this need for control. Even as public cloud applications represent a massive 59.2% of revenue, a huge chunk of multi-tenant data center revenue (~53.4%) still comes from retail colocation, where companies rent physical space to run their own isolated hardware. This trend, detailed in a multi-tenant data center report, shows the deep-seated demand for true isolation.
Of course, this premium approach comes with a premium price tag. Provisioning, managing, backing up, and updating a separate database for every single customer is both expensive and operationally intensive.
Comparison of Multi-Tenancy Models
Choosing the right model is about balancing your specific needs for isolation, cost, and complexity. This table breaks down the key differences to help you decide which path makes the most sense for your application.
Model | Data Isolation | Cost Efficiency | Development Complexity | Best For |
|---|---|---|---|---|
Shared Schema | Low (Application-level) | Very High | High (Requires strict query logic) | B2C apps or B2B SaaS with many small tenants. |
Isolated Schema | Medium (Database-level) | High | Medium (Schema management) | B2B SaaS with a mix of tenants, some needing customization. |
Isolated Instance | Very High (Infrastructure-level) | Low | Low (Once automated) | Enterprise SaaS, highly regulated industries, or customers with strict security needs. |
Ultimately, the model you choose sets the foundation for how your application will scale and operate. Many companies even use a hybrid approach, starting new customers on a shared model and offering an upgrade to an isolated instance for a higher price.
Weighing the Benefits and Trade-Offs of Multi-Tenancy
Deciding to go with a multi-tenant architecture is a major strategic move. It's usually driven by some seriously compelling economic and operational perks. For most SaaS companies today, the case for building on a shared foundation is pretty hard to argue with.
But all that efficiency doesn't come for free. It brings its own brand of challenges that require smart planning and solid engineering. You have to understand both sides of this coin before you lock yourself into a model that will shape your product's cost, scale, and security for years to come.
The Upside: Why Everyone Loves Multi-Tenancy
The biggest reason to adopt multi-tenancy boils down to powerful economic efficiency. When you pool resources, you create a system that's just plain cheaper to build, run, and grow. This all rests on three main ideas.
Massively Lower Operational Costs: Think about it: instead of spinning up a separate server, database, and application instance for every single customer, you run one unified stack. That means fewer servers to manage, less software to license, and resources used to their fullest potential. Your infrastructure bill shrinks.
Painless Maintenance and Upgrades: When it’s time to push a software update or patch a security hole, you do it once. That’s it. The fix instantly rolls out to every tenant on the platform. This completely sidesteps the operational nightmare of trying to update hundreds or even thousands of separate environments.
Onboard and Scale in a Flash: Adding a new customer becomes as simple as creating a new entry in a database. You aren't building an entire environment from the ground up. This makes onboarding almost instantaneous and fully automated, letting your business grow its customer base without your operations team growing at the same rate.
A well-architected multi-tenant system does more than just cut costs. It frees up your team to focus on building great features instead of getting bogged down in infrastructure management.
This shift isn't just a trend; it's a massive industry-wide movement. Multi-tenant data centers (MTDCs) now dominate the landscape, with a global market valued somewhere between USD 38–68 billion in the mid-2020s. And it’s not slowing down. Forecasts predict that market could swell to USD 185 billion by 2035. If you're interested in the numbers, you can dig into a comprehensive MTDC market report to see the full scope of this growth.
The Downside: The Critical Trade-Offs and Risks
While the benefits are huge, they introduce complexities you have to tackle head-on. Ignoring these risks can lead to serious performance bottlenecks, security breaches, and operational headaches down the road.
It's Just More Complex
Let's be honest: building a secure and reliable multi-tenant app is a lot harder than building a single-tenant one. Your developers have to be incredibly careful, implementing logic that ensures every single request is correctly filtered for the right tenant. This demands a deep understanding of isolation techniques and adds more potential failure points if you're not meticulous.
The "Noisy Neighbor" Problem
In any shared space, you run the risk of one person hogging all the resources. The same is true here. If one of your tenants decides to run a massive data export, they could monopolize the CPU and database connections, slowing down the entire application for everyone else. Fighting this means putting sophisticated resource limits, monitoring, and throttling in place to ensure everyone plays nice.
A Bigger Security and Compliance Burden
When you have multiple customers' data living in the same database, the security stakes are sky-high. One tiny bug in your data isolation logic could cause a catastrophic data breach, exposing one tenant's sensitive information to another. This means your security measures have to be rock-solid, with rigorous code reviews and constant testing to make sure those tenant walls are impenetrable. It also complicates things when you need to meet compliance standards for industries like healthcare or finance, where strict data isolation isn't just a good idea—it's the law.
Mastering Security and Data Isolation
When you're building a multi-tenant application, you’re making one non-negotiable promise to your customers: their data will stay completely private. Getting this wrong isn't just a technical glitch; it's an existential threat to your business. A single data leak can shatter trust instantly. This means you have to go beyond just talking about security and implement specific, battle-tested mechanisms that build real walls between tenants.
The good news is that a well-architected multi-tenant system can be just as secure as a single-tenant one. It all comes down to a defense-in-depth approach, protecting data at every single stage. Let's dig into the core technologies that make this possible.

Row-Level Security: The Bedrock of Data Segregation
Picture a giant database table holding sales data from a hundred different companies. The most critical security challenge is making sure that when a user from "Company A" runs a report, they only see rows belonging to Company A. This is exactly what Row-Level Security (RLS) is designed for.
RLS is a database-level feature that enforces security policies directly on the data itself. Think of it as an automatic, non-negotiable filter. Whenever a user runs a query, the database first checks who they are and then invisibly adds a condition—like WHERE tenant_id = 'company_a'—before sending back any results.
This is a game-changer because it shifts the responsibility for data filtering from your application code to the database. Your developers no longer have to remember to add that
WHEREclause to every single query, which drastically cuts down the risk of human error leading to a catastrophic data leak.
Managing Access with SSO and SAML
While RLS is fantastic at protecting data inside the database, you first need a rock-solid way to control who can even get into the application. This is where modern authentication and authorization protocols come in, making sure users are who they claim to be and have the right permissions.
Single Sign-On (SSO): This lets users log into your app using the credentials they already have for their company (like Google Workspace or Microsoft 365). It makes life easier for your customers by centralizing user management and tightens security by reducing password reuse.
Security Assertion Markup Language (SAML): This is the open standard that actually makes SSO work. It securely passes authentication and authorization information between an identity provider (like Okta) and your application, verifying a user’s identity without ever sharing their actual password.
For any multi-tenant app, these tools are essential. They empower each tenant to manage their own user access securely, enforce their own password rules, and instantly cut off access when an employee leaves.
A Multi-Layered Encryption Strategy
True data isolation isn’t just about access controls; it also demands end-to-end encryption. You have to protect data at every point in its journey, leaving zero gaps for an attacker to exploit. A solid encryption strategy really boils down to two key parts.
Encryption in Transit: This protects data as it travels between a user's browser, your application servers, and the database. It's typically handled by Transport Layer Security (TLS), the standard that powers HTTPS. TLS ensures that if anyone intercepts the network traffic, all they'll see is unreadable gibberish.
Encryption at Rest: This secures data while it's physically stored on a disk, whether in your database or in backups. It prevents anyone from accessing the information even if they somehow managed to get their hands on the server hardware. Most modern cloud databases use powerful encryption standards like AES-256 to protect data at rest by default.
For any multi-tenant system, it's critical to understand these modern data security concepts to build a truly secure environment. This also has major implications for regulatory compliance; if you're building a SaaS platform, knowing your obligations is a must. For a deeper dive, check out our guide on achieving GDPR compliance for SaaS BI. By layering RLS, SSO/SAML, and comprehensive encryption, you can build a fortress around each tenant's data.
Managing Operations and Scale in a Multi-Tenant System
Building a multi-tenant system is one thing; keeping it running smoothly as you scale is a completely different beast. The challenges you face with ten customers are nothing like the ones you'll hit at ten thousand. Your focus shifts from just "keeping the lights on" to actively managing performance, ensuring fair resource use, and shipping updates without your customers ever noticing.
Scaling a shared system isn't just about throwing more servers at the problem. It’s about building an intelligent, resilient architecture that can handle whatever your customers throw at it while delivering a consistently great experience for everyone.
Scaling Strategies for Fair Resource Use
One of the classic headaches in any multi-tenant environment is the "noisy neighbor." This is what happens when one tenant’s sudden, massive workload—like a huge data import or a complex analytics query—hogs all the resources, slowing down the experience for every other tenant on the same infrastructure.
To keep things fair and stable, engineering teams have a few go-to strategies:
Dynamic Resource Allocation: Modern container orchestration tools are great for this. The system can automatically spin up more CPU or memory for a tenant who needs it, and just as importantly, scale it back down when the spike is over. It’s an elastic approach that makes sure you’re not overprovisioning.
Load Balancing: A smart load balancer is your best friend here. It distributes incoming traffic evenly so no single server gets slammed and becomes a bottleneck. We actually have a deep dive on how hash partitioning improves load balancing if you want to get into the weeds on that.
Rate Limiting and Throttling: This is all about setting sensible guardrails. By capping API calls or database queries per tenant, you ensure that no single customer can accidentally (or intentionally) bring down the entire system.
The Importance of Tenant-Aware Monitoring
You simply can't manage what you can't measure. Generic monitoring that just tells you about overall server health is practically useless in a multi-tenant world. What you really need is tenant-aware monitoring, which gives you a clear view into what each individual customer is doing and how many resources they're consuming.
This level of detail is a game-changer. It lets you bill customers fairly based on their actual usage, helps you pinpoint the root cause of a performance issue for a specific user, and shows you which customers are really pushing the system's limits. That data is gold for capacity planning and making smart infrastructure investments.
The operational demand for this kind of shared infrastructure is exploding. Recent data shows that the multi-tenant data center supply in North America hit a staggering 8,155 megawatts (MW) in just six months—a 43.4% jump from the previous year. As detailed in CBRE's data center trends report, these numbers show just how much investment is pouring into powering these massive shared systems.
Key Insight: Without tenant-specific metrics, your support team is flying blind. They have no way of knowing if an issue is a system-wide outage or just a problem affecting a single, power-hungry tenant.
Deploying Upgrades with Zero Downtime
In the world of SaaS, scheduled maintenance windows are dead. Your customers expect the service to be up and running 24/7, period. This turns every deployment, from a minor bug fix to a major database schema change, into a high-stakes operation.
Pulling off zero-downtime deployments usually means adopting advanced techniques like blue-green deployments or canary releases. These strategies let you roll out new code to a small group of tenants first. You can watch for any issues, and if all looks good, gradually release it to everyone else. If something goes wrong, you can roll it back in an instant. For anyone looking at different architectural patterns to tackle these challenges, understanding the pros and cons of microservices architecture is a great place to start.
Bringing It All Together with Embedded Analytics
So, where do all these architectural models and security protocols actually come into play? Embedded analytics is the perfect real-world example. For any SaaS company, offering sharp, customer-facing dashboards right inside the application is a massive differentiator. But pulling that off securely for hundreds—or even thousands—of customers is a nightmare without a solid multi-tenant architecture.
This is where the rubber meets the road. Rather than spending months (or years) building a multi-tenant business intelligence (BI) layer from scratch, smart product teams turn to specialized platforms. These tools are built specifically to solve the isolation and security puzzles we've been talking about.

A Practical Path to Implementation
Let's say you want to give each customer a personalized dashboard showing their specific usage stats. A purpose-built analytics platform can handle the heavy lifting, connecting to your database and managing the security logic needed to serve every single tenant correctly.
This approach brings everything we've discussed full circle. It shows how a deep understanding of multi-tenancy lets you ship powerful features that users genuinely value, turning a complex architectural decision into tangible business impact.
Here’s what that process usually looks like:
Secure Connection: The analytics platform connects to your production database using read-only credentials. This is a critical first step, ensuring it can never accidentally change your core data.
Define Tenant Boundaries: Next, you tell the system how to identify your tenants. This is often as simple as pointing it to the
tenant_idcolumn in your tables, which allows for automatic data segregation.Apply Row-Level Security: You then set up security rules that enforce a simple, non-negotiable principle: a user from Tenant A can only see data where the
tenant_idis 'A'.Embed via Signed Tokens: Finally, you embed the dashboards into your app using secure, signed tokens. These tokens act like a passport, carrying the user's identity and
tenant_idto tell the analytics layer precisely what data to show them.
By using a dedicated solution, you're essentially adopting a battle-tested multi-tenant security model. This frees your team to focus on building great dashboards instead of reinventing the wheel on complex data permission systems.
Platforms like Querio are designed specifically for customer-facing embedded analytics, offering the isolation, security, and performance you need to deliver a top-notch experience. It's a strategy that not only gets you to market faster but also ensures your analytics are scalable and secure right from the start.
Frequently Asked Questions About Multi-Tenant Architecture
Even after getting familiar with the different models and their trade-offs, a few common questions always seem to pop up when teams start thinking about building a multi-tenant product. Let's clear up some of the most common points of confusion.
Is Multi-Tenancy the Same as Virtualization?
Not at all—they solve different problems at different layers of the tech stack.
Think of virtualization like building several distinct houses on one piece of land. A hypervisor slices up a single physical server into multiple virtual machines (VMs), and each VM gets its own dedicated operating system. It's infrastructure-level isolation.
Multi-tenancy, on the other hand, is more like designing secure, private apartments within a single large building. It works at the application level. One instance of the software serves all your customers, but with logical walls between them. The two concepts often work together, though; it's very common to run a multi-tenant app on a virtual machine.
What Is the Biggest Security Risk?
By far, the biggest risk is a data breach where one tenant sees another tenant's data. This nightmare scenario almost always comes down to a bug in the application code or a flaw in the isolation logic. A single bad SQL query that forgets a WHERE tenant_id = ? clause could expose everything.
The absolute necessity of preventing data leakage cannot be overstated. Rigorous testing, secure coding practices, and strong database-level isolation techniques like Row-Level Security (RLS) are non-negotiable to build a trustworthy platform.
A close second is the "noisy neighbor" problem. This happens when one tenant's massive workload slows down the application for everyone else, which is more of a performance and reliability risk than a data security one.
How Does Multi-Tenancy Affect Application Performance?
It’s a classic double-edged sword that you have to manage carefully.
On the bright side, pooling resources is incredibly efficient. Your infrastructure isn't just sitting idle waiting for one customer to do something. This leads to better overall system responsiveness and, of course, lower operational costs.
But the "noisy neighbor" issue is a constant threat. One tenant running a huge report or a complex query can hog CPU, memory, or database connections, dragging performance down for everybody. The best multi-tenant systems get ahead of this with:
Resource Governance: Implementing fair-use policies and throttling.
Rate Limiting: Capping how many requests a tenant can make over a specific time.
Tenant-Aware Monitoring: Keeping a close eye on who is using what, so you can spot resource hogs before they cause a system-wide slowdown.
Your architectural choice makes a huge difference here, too. A fully isolated database will naturally give a tenant more predictable performance than a database where everyone shares the same tables.
Ready to deliver powerful, secure, and scalable analytics to your customers? Querio's embedded analytics platform is built with multi-tenancy at its core, providing robust data isolation, row-level security, and signed embeds out of the box. Learn how to ship customer-facing dashboards in minutes, not months.

